Introduction
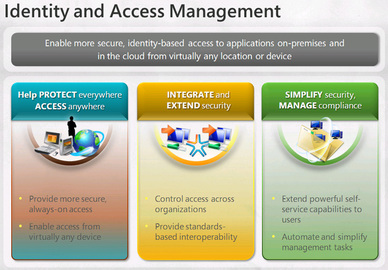
With high competition and the amalgamation of information technology into business, many companies and business entities now look for secure environment to increase their business effectiveness. This is why many companies are releasing the potential of Access Management Identity systems. Many organizations now seem to be in the process of divesting, merging and downsizing themselves. This translates into a number of people leaving and entering the organization. It creates a situation for the organizations where they want to control the access to their networks and resources. So that right people are accessing the right resources for the right reasons. This is the fundamental reason of the use of Access management identity in helping the company address this dilemma. There are tools and controls that help you authorize and regulate the employees to access the company’s network.
History
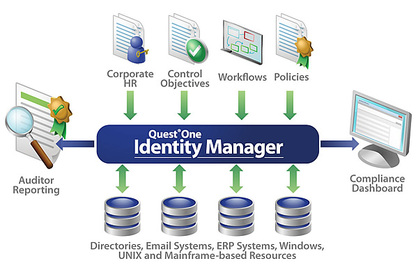
There are a number of tools that can help an organization manage the Access management identity systems. One of these is the Hitachi ID Identity Manager. This software not only assists in the identity information but also in passwords and in altering the database. This helps the Human resource department to make changes to the access controls with respect to employees leaving and entering the organization. Another tool for effective administration of access management identity is the Quest One Identity Solution. As the name suggests, the Quest One Identity Solution helps in streamlining the process of the access and identity management of organizations. It does so by creating usernames and passwords that can be used for multiple applications and resources of the company. The ease with which businesses can manage passwords, reset the lost ones and implement security protocols makes it a favorite among organizations.
Features
To understand Access and identity management systems it is imperative that the concept of compliance rules is realized along with it. These are the rules or protocols that the information technology department implements with the consultation of the senior management and with compliance to government regulations. These rules help in determining how the Access management identity system works for the individuals involved. One of these rules is the “segregation of duties”. This means that if there are three employees accessing the resources, two of them would be able to access it from anywhere whereas the third will only do so from the office. While the third one will also be delegated to make changes into the database. Other types of compliance rules for access and identity management systems are the access controls. These rules are established when there is fear of identity theft or if the information involved is of significance. Other types of compliance rules are for notification and alerts.
Tips and comments
Access management identity is essential for business to have agility in the highly competitive markets. Systems need to be protected for more coherent and effective sharing of information and utilization of company resources. It is therefore imperative for many businesses to get a protected system for a streamlined information access and management of company resources to succeed in the competition.
Comments
Most Recent Articles
-
What you need to know about anthrax
Anthrax is a serious, life-threatening, infectious disease caused by the gram-positive, spore-forming bacteria called Bacillus anthracis. Under the microscope, these bacteria appear like lar...
-
Information on Management Systems
In the rapidly evolving world of technology, we have to encounter with a variety of IT issues and these are getting complicated day by day. With so much technology around us, the demand for ...
-
5 Things You Must Know About Jobs Management Consulting
When it comes to management consulting jobs, there are a number of things that one needs to be aware of. These are basically the key pointers that will enable one to effectively perform the ...
-
10 Amazing Tips For Management Practice
Management can be described as the act of getting people together to accomplish set objectives and goals using the given resources effectively and efficiently. It involves coordination and o...
-
Organization Of Executive Management
The structure of every organization has different levels based on management, and these levels are between executive and employees who are in the front line. The task of executive management...
-
Management Courses in Leadership
There are various prestigious institutions that provide impeccable management courses in leadership. You can select the one for you by knowing whether it really stands out and has got someth...
-
Discover 8 Tips For College Management
Many people enter college thinking that the pressures and stresses will not be problem for them. They later realize that grades are slipping or they are missing classes. This is v...
-
Information on Management Technology
Information technology is a discipline directly linked to computers, telecommunication, the retrieval of important data, and its transmission and storage. Management in IT is a branch where ...
-
What Are Stress Diseases?
What is stress and how does it affects an individual’s health? This is a common question nowadays. Mental health professionals define stress as the physiological and psychological con...
-
Benefits Of Management Strategy
Management strategy is very imperative in any business that you are undertaking. If you lack a management strategy for your business then it is very possible that you will not be able to han...
-
Rise To the Tip Management Access
Access management generally refers to the regulation of interchanges, driveways, intersections and median openings to a roadway. Access Management, abbreviated as AM is the keyed up manageme...
-
Rules For Solution Management
We always hear about solution management and most people don’t know what that means. Some take it literary as the management of solutions found for the company and choosing the one tha...
-
Jobs in Sales Management
The sales manager is responsible for the company's sales force, the hiring and training of employees. Planning, creating, implementing, and reviewing the entire process depends on experience...
-
What Is An Application For Management
Almost every career requires some sort of management. With the rapidly increasing technology, management is becoming tough. Regardless of the field, management applications have become essen...
-
Tips And Ideas For Practice Management
If you want to start a business, or to accomplish your dream of making a great company you should learn for the beginning a few tips and ideas for practice management. First important issue ...